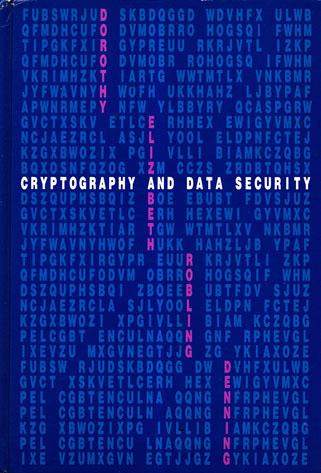
Cryptography and Data Security
by Dorothy Elizabeth Robling Denning
Publisher: Addison-Wesley 1982
ISBN/ASIN: 0201101505
ISBN-13: 9780201101508
Number of pages: 419
Description:
The goal of this book is to introduce the mathematical principles of data security and to show how these principles apply to operating systems, database systems, and computer networks. The book is for students and professionals seeking an introduction to these principles.
Download or read it online for free here:
Download link
(19MB, PDF)
Similar books
 Forensic Analysis of Database Tampering
Forensic Analysis of Database Tamperingby Kyriacos E. Pavlou, Richard T. Snodgrass - University of Arizona
The text on detection via cryptographic hashing. The authors show how to determine when the tampering occurred, what data was tampered, and who did the tampering. Four successively more sophisticated forensic analysis algorithms are presented.
(21307 views)
 Rethinking Public Key Infrastructures and Digital Certificates
Rethinking Public Key Infrastructures and Digital Certificatesby Stefan A. Brands - The MIT Press
In this book Stefan Brands proposes cryptographic building blocks for the design of digital certificates that preserve privacy without sacrificing security. Such certificates function in much the same way as cinema tickets or subway tokens.
(11710 views)
 The Protection of Information in Computer Systems
The Protection of Information in Computer Systemsby J.H. Saltzer, M.D. Schroeder - MIT
This tutorial paper explores the mechanics of protecting computer-stored information from unauthorized use or modification. It concentrates on those architectural structures that are necessary to support information protection.
(10511 views)
 Security Enhanced Applications for Information Systems
Security Enhanced Applications for Information Systemsby Christos Kalloniatis - InTech
Designing and implementing security enhanced systems is of vital importance. This book aims to present a number of innovative security enhanced applications. It involves cases based on the standalone, network and Cloud environments.
(9799 views)