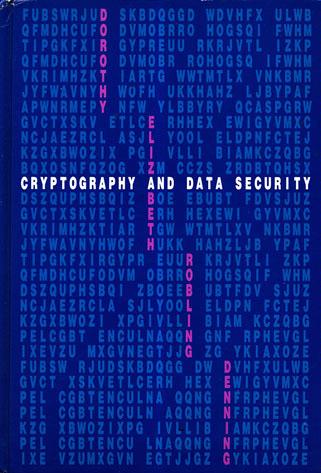
Cryptography and Data Security
by Dorothy Elizabeth Robling Denning
Publisher: Addison-Wesley 1982
ISBN/ASIN: 0201101505
ISBN-13: 9780201101508
Number of pages: 419
Description:
The goal of this book is to introduce the mathematical principles of data security and to show how these principles apply to operating systems, database systems, and computer networks. The book is for students and professionals seeking an introduction to these principles.
Download or read it online for free here:
Download link
(19MB, PDF)
Similar books
 Rethinking Public Key Infrastructures and Digital Certificates
Rethinking Public Key Infrastructures and Digital Certificatesby Stefan A. Brands - The MIT Press
In this book Stefan Brands proposes cryptographic building blocks for the design of digital certificates that preserve privacy without sacrificing security. Such certificates function in much the same way as cinema tickets or subway tokens.
(11667 views)
 Security and Privacy in Wireless and Mobile Networks
Security and Privacy in Wireless and Mobile Networksby Georgios Kambourakis, et al. - MDPI AG
Dedicated to the security and privacy aspects of mobile networks, wireless communications, and their apps. The focus is on the security and privacy of mobile software platforms and the increasingly differing spectrum of mobile or wireless apps.
(7270 views)
 Policing Cyber Crime
Policing Cyber Crimeby Petter Gottschalk - BookBoon
From the table of contents: Introduction; Cyber Crime Defined; Cyber Crime Cases; Child Grooming Case; Crime Protection; Corporate Reputation; Knowledge Management; Intelligence Strategy; Crime Investigations; References.
(14268 views)
 A Guide to Claims-Based Identity and Access Control
A Guide to Claims-Based Identity and Access Controlby Dominick Baier, at al. - Microsoft Press
This book gives you enough information to evaluate claims-based identity as a possible option when you're planning a new application or making changes to an existing one. It is intended for any architect, developer, or IT professional.
(12750 views)