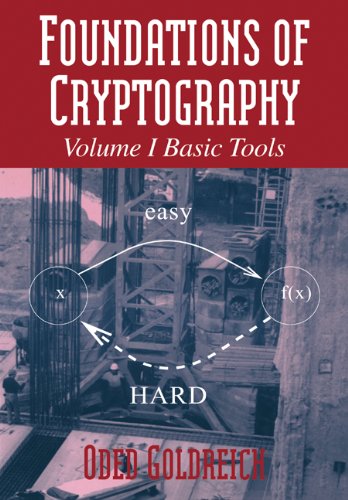
Foundations of Cryptography
by Oded Goldreich
Publisher: Cambridge University Press 2007
ISBN/ASIN: 0521035368
Number of pages: 396
Description:
The book presents complexity research which gives the mathematical underpinnings for cryptography; this includes one-way functions, pseudorandom generators, and zero-knowledge proofs. Throughout, definitions are complete and detailed; proofs are rigorous and given in full.
Download or read it online for free here:
Download link
(multiple PS files)
Similar books
 A Graduate Course in Applied Cryptography
A Graduate Course in Applied Cryptographyby Dan Boneh, Victor Shoup - cryptobook.us
This book is about constructing practical cryptosystems for which we can argue security under plausible assumptions. The book covers many constructions for different tasks in cryptography. For each task we define a precise security goal ...
(5867 views)
 Hacking Secret Ciphers with Python
Hacking Secret Ciphers with Pythonby Al Sweigart
The book teaches complete beginners how to program in the Python programming language. The book features the source code to several ciphers and hacking programs for these ciphers. The programs include the Caesar cipher, transposition cipher, etc.
(22291 views)
 Visual Cryptography and Its Applications
Visual Cryptography and Its Applicationsby Jonathan Weir, WeiQi Yan - BookBoon
Visual cryptography provides a technique by which one secret can be distributed into two or more shares. When the shares are xeroxed onto transparencies and then superimposed, the original secret can be discovered without computer participation.
(10572 views)
 Lecture Notes on Cryptography
Lecture Notes on Cryptographyby Shafi Goldwasser, Mihir Bellare
This is a set of lecture notes on cryptography for a one week long course on cryptography taught at MIT. The thread followed by these notes is to develop and explain the notion of provable security and its usage for the design of secure protocols.
(15013 views)